Sensors, actuators and other IoT devices communicate with applications running on computer servers over IoT networks. These servers may be on-premises or in the cloud and there are a growing number of attacks on them where the IoT devices themselves are providing ‘windows’ into the networks.
To prevent such attacks, there are two fundamental requirements:
- IoT devices, most of which are designed around microcontrollers, must have unique, immutable, and unforgeable identities so that applications can be certain which devices they’re communicating with.
- The messages must be encrypted and decrypted so that only the intended recipients can understand them. Cryptographic keys and digital certificates serve this purpose.
The importance of the root-of-trust
A root-of-trust, or RoT, comprises a device’s identity and its cryptographic keys. It’s a foundational requirement for a secure IoT network. The identities and keys are random numbers. The more random they are, the harder the device is to hack.
A lot of IoT devices rely on these random numbers being injected into their microcontrollers’ memories or external memory chips, where they are stored. It’s an expensive process and stored keys are vulnerable to theft or leakage so, while the method is commonly used, it is not the most secure.
If silicon chips can generate identities and keys from the fabric of the silicon, it’s more secure. In recent years, several semiconductor manufacturers have produced chips that can do this using Physical Unclonable Functions, or PUFs. During CMOS chip manufacturing, the thickness of the oxide layer exhibits random variations. At microscopic geometries, these variations can be used as the basis for PUFs to generate random numbers that become each chip’s unique identity, or fingerprint. Some PUFs can also produce cryptographic keys in silicon, eliminating the need for key injection.
Once you have established the RoT within an IoT device, you need to find a secure way to connect it to server-hosted services and applications.
Automation eliminates the complexity of chip-to-cloud connectivity
Cryptography is complicated, creating a barrier to IoT deployment. The only way to address this challenge is with a software platform that presents a simple, easy-to-understand user interface.
Several such platforms have come to market in recent years. QuarkLink is an example of one of the most comprehensive due to its ability to handle secure provisioning, onboarding to servers, and lifetime management of IoT devices. Here’s how it works.
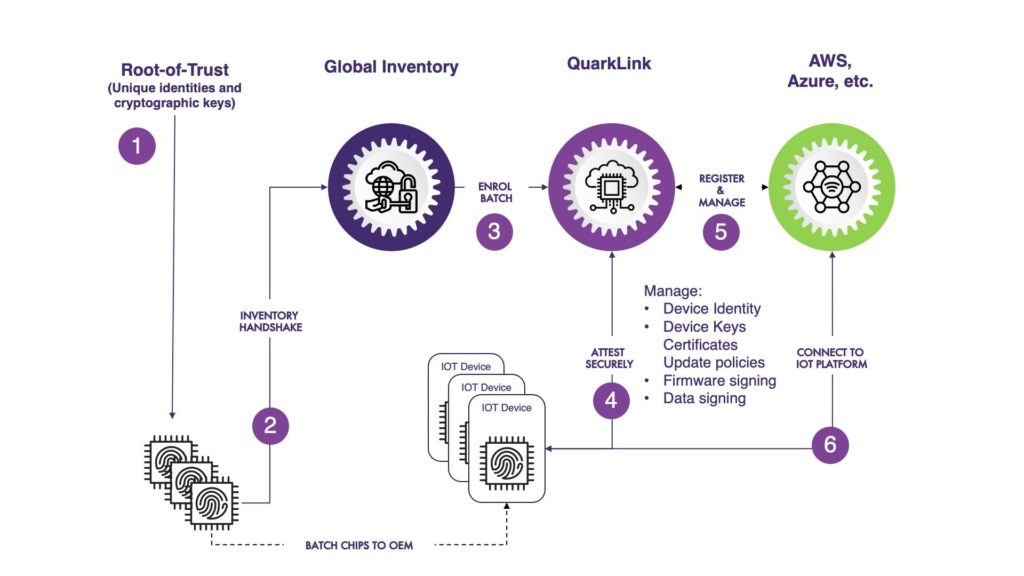
Figure 1: IoT security process overview from silicon-to-server
First, the device identities are uploaded to a global inventory platform where they can be accessed by QuarkLink. This platform can be on-premises or in the cloud. A four-part process follows:
- The pre-defined server policy is chosen from a drop-down menu. It’s usually AWS, Azure or Mosquito but QuarkLink can be used with others, including on-premises servers. This avoids the need for users to have to configure complex server policies.
- A batch of device identity keys is checked against the identification numbers on the global inventory for a match. This ensures that the correct devices are being connected to the server.
- When a device needs to onboard, it makes a request to QuarkLink which sets up a secure communications link using the industry-standard Transport Layer Security (TLS) protocol. Through this secure link, the devices are asked to prove their identities.
- With that done, encrypted connections are established then the devices can communicate securely with the server-hosted applications.
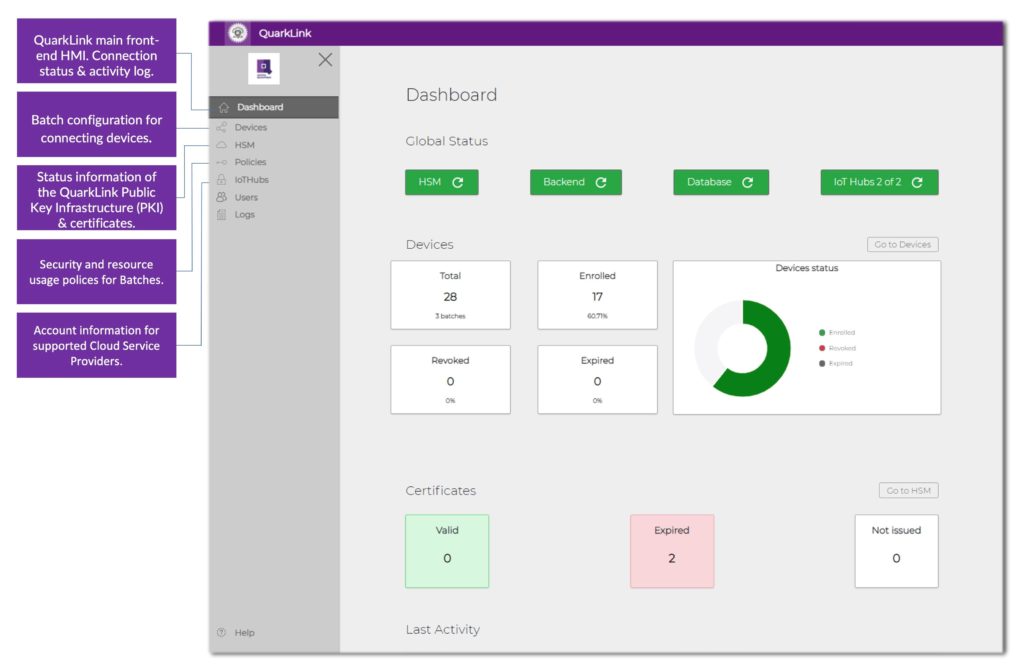
Figure 2: Via this simple interface, the complexities of device provisioning, onboarding and lifetime management are reduced to a few key clicks
Platforms such as QuarkLink make it easy to manage security throughout the operating life of IoT devices. They manage certificates and security policies, facilitate firmware signing and encryption for secure over-the-air (OTA) updates, and manage key and certificate renewal, which is sometimes needed after a system fault or external interruption. Devices are easily removed from the network if they fail or are compromised.
Concluding cloud security
A key reason for the slow adoption of IoT is the complexity of security.
Implementation can take months and many projects fail altogether. Software that automates all this complexity is the only way forward, reducing tasks to a simple user interface that embedded engineers and IoT network operators can learn quickly and use with confidence. With the right platform, no cryptographic skills or knowledge are needed.
– Originally written by Chris Jones, IoT Security Specialist, Crypto Quantique –
Following a 28-year career in project management and field applications engineering, Chris spent two years as a senior application engineer at Secure ThingZ in Cambridge, UK, working in IoT security. He joined Crypto Quantique in May 2020. Chris holds a BSc in electrical and electronic engineering from the University of Coventry, UK.