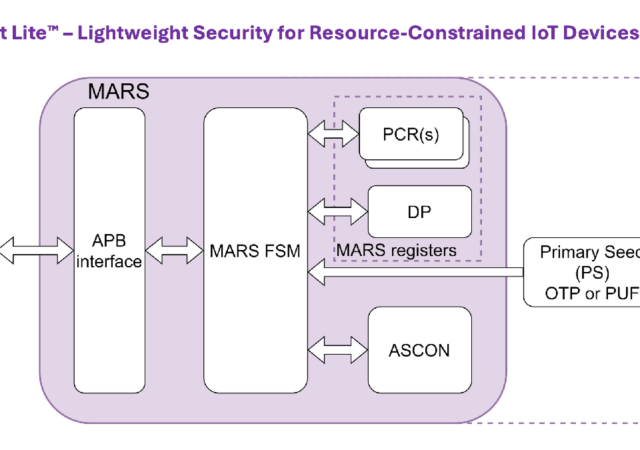
Crypto Quantique has announced a new lightweight root-of-trust (RoT) IP block to enable security feature implementation in resource-constrained microcontrollers and IoT devices. Called QRoot Lite, the implementation complies to the Measurement and Attestation RootS of Trust (MARS) specification developed by…
3 reasons website traffic analysis can help protect your website
As a digital business owner, one of your priorities will be analysing the traffic coming into your website, and monitoring just how successful your online presence is. The more traffic coming in, the clearer it is that your digital marketing…
Encrypted Communication
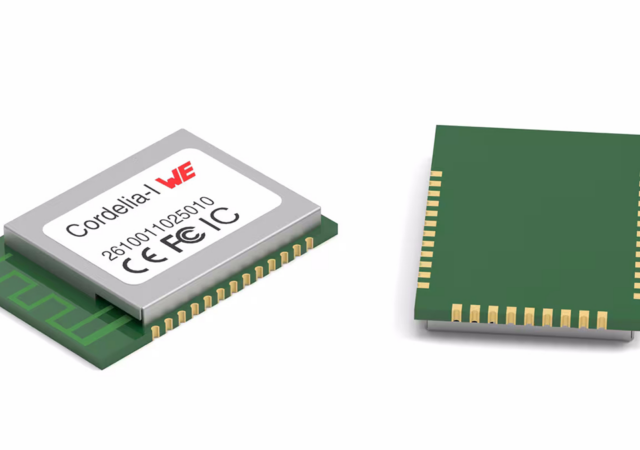
Würth Elektronik introduces its new Cordelia-I Wi-Fi module, specifically designed for secure IoT and ‘Edge Computing’ applications. This versatile module is ideal for applications in Industry 4.0, smart city / smart home, eMobility, smart agricultural, and medical devices, to name…
Cynomi report cites offering vCISO services as a growth opportunity
Cynomi, a provider of virtual Chief Information Security Officer (vCISO) platforms for managed service providers (MSPs) and managed security service providers (MSSPs), has released its 2024 State of the Virtual CISO report. The findings highlight a significant gap between the…
AWS and IoT: Enabling scalable IoT networks
Building a scalable and secure IoT solution can be challenging, particularly when it comes to managing large volumes of data, ensuring device security and maintaining reliable connectivity. Amazon Web Series (AWS), a Cloud computing platform, looks to address all of…
2N discusses PSTI standards
2N Telecommunications’ access systems, along with its range of products, comply with British safety standards, including the Product Security and Telecommunications Infrastructure (PSTI) Act, which came into effect on 29th April 2024. This legislation introduces enhanced cyber security measures for…
Keysight to participate in Joint Cyber Defense Collaborative
Keysight Technologies has announced its participation in the Joint Cyber Defense Collaborative (JCDC), further strengthening its partnership with the US government to bolster the nation’s cybersecurity resilience. With two decades of experience in cybersecurity testing and threat intelligence research, Keysight…
Genians widens focus to include IoT security
Genians, a provider of NAC-driven Zero Trust Network Access (ZTNA) solutions, is strengthening its commitment to securing the digital future by broadening its global focus to include IoT and critical infrastructure security. As the digital world evolves, the rapid expansion…
Luminys, Foxlink and MediaTek partner on AI-powered security
Luminys Systems, along with its parent company, Foxlink, has announced a strategic partnership with global semiconductor company MediaTek. This collaboration is set to usher in the next generation of AI-driven video security solutions by integrating MediaTek’s state-of-the-art chip technology, Foxlink’s…
Cato Networks publishes report mapping threat landscape
Cato Networks has recently released the Q2 2024 Cato CTRL SASE Threat Report, shedding light on the evolving threat landscape across several critical areas: hacking communities and the dark web, enterprise security, and network security. This report draws its insights…